TCP vs UDP: A Comprehensive Guide to All Key Differences
If you have ever thought about why some sites load in no time while others buffer constantly—or why your online game lags despite having a quick connection—the solution generally comes down to one option: TCP vs UDP. These two protocols power virtually everything you do on the internet, ranging from searching and email to live video calls and challenging gaming. Knowing about what is the difference between TCP and UDP protocol is not only a technical expertise—it has real business consequences, mainly when selecting between scalable cloud hosting solutions and premium GPU compute resources.
In this complete blog, we will just break down TCP vs UDP which is better, check out when to use TCP vs UDP reliability, and show how the true protocol—combined with the appropriate infrastructure—can revolutionize your processes.
What Is TCP?
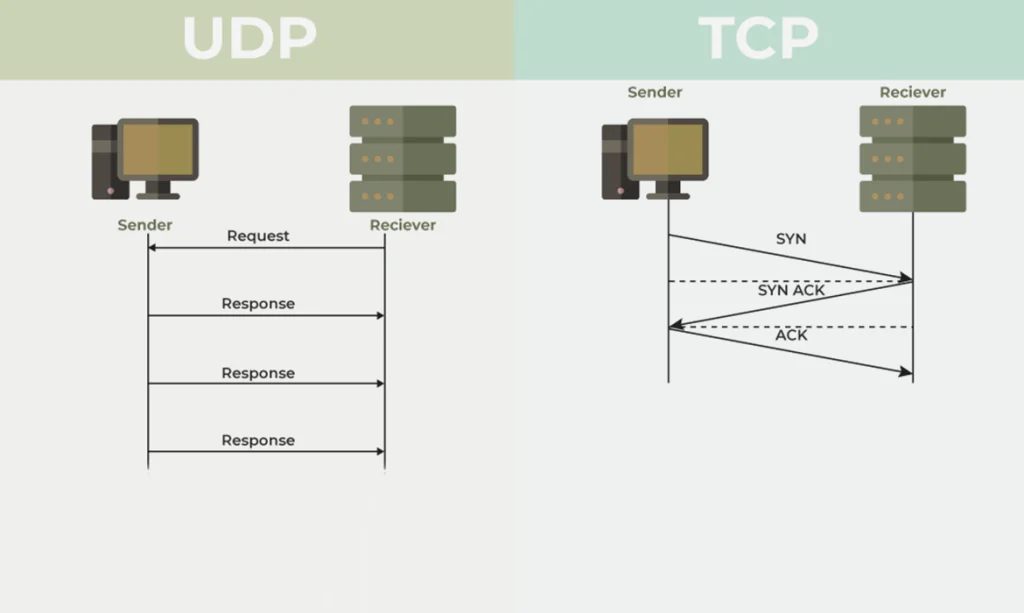
TCP, which stands for transmission control protocol, is the dependable workhorse of the whole Internet. Before any data is sent, it establishes a connection through a three-way handshake, ensures every packet arrives, and reassembles them in the correct order. Think of it just like sending a verified package—tracked, allocated, and certified.
Key characteristics of TCP: connection-oriented sessions, automatic retransmission of lost packets, in-order delivery, and robust error-checking with flow control.
TCP reliability makes it an important choice where data addition is non-negotiable: banking transactions, file transfers, email, and web browsing (HTTP or HTTPS). If you absolutely cannot afford to lose a single byte, TCP is your protocol.
What Is UDP? (User Datagram Protocol)
UDP, which stands for user datagram protocol, is TCP’s quicker, less careful sibling. It fires packets without setting up a specific connection, without waiting so long for responses, and without retransmitting the lost data. That sounds quite unsafe—but for the appropriate use cases, it’s exactly what you wish for.
TCP vs UDP speed difference: UDP wins in all ways. Without clasping and responses overhead, UDP pushes data drastically quickly. The tradeoff is that some of the packets may drop or arrive out of order, and the app must manage that.
Real-time apps thrive on UDP. If you miss a frame in a video call, you don’t want the system frozen while it retransmits old data. You’d rather just move on.
TCP vs UDP Reliability: Quick Comparison
|
Feature |
TCP |
UDP |
|
Connection |
Connection-based |
Connectionless |
|
Reliability |
Guaranteed delivery |
No specific guarantee |
|
Speed |
Slower (overhead) |
Quicker (low overhead) |
|
Error Checking |
Yes (retransmission) |
General checksum only |
|
Ideal For |
Web, email, banking |
Gaming, streaming, VoIP |
|
Packet Ordering |
Yes |
No |
TCP vs UDP for Gaming
In the case of TCP vs UDP for gaming, UDP rules everywhere—and for genuine reason. In the situation of online games, even milliseconds are very important. TCP’s retransmission logic adds interruptions that can cost you the whole match.
Games like Fortnite, Valorant, and Call of Duty use UDP to keep gameplay fluid. If a movement packet is lost, the game extrapolates from the last known position rather than freezing to wait. Even so, these games use TCP for login, save data, and match loading — proving both protocols have their place.
This is exactly where how GPU servers can benefit your business becomes relevant. Gaming companies running on premium GPU compute resources process physics, AI, and rendering at scale — while UDP game servers handle real-time player data simultaneously.
TCP vs UDP for Streaming
TCP vs UDP for video streaming depends entirely on what you’re streaming.
For live streaming VOD platforms and real-time broadcasts, UDP is the traditional choice. Protocols like RTP and WebRTC are built on UDP because low latency beats perfect delivery. A dropped frame is far less annoying than a buffering spinner.
For on-demand video (Netflix, YouTube), TCP is dominant. DASH and HLS streaming use HTTP over TCP, where the buffer makes perfect delivery worthwhile.
The lines are blurring with QUIC (HTTP/3), which delivers TCP-like reliability over UDP. Modern hosting providers for websites increasingly support QUIC-enabled stacks for this reason — giving platforms the best of both worlds.
When to Use TCP vs UDP
Simple rule: If losing data breaks your app — use TCP. If losing data just causes a minor glitch — use UDP.
Use TCP for e-commerce platforms, banking apps, email servers, file transfers, and REST APIs running on scalable cloud hosting solutions. Use UDP for multiplayer games, live video conferencing, IoT sensor networks, DNS lookups, and real-time streaming.
Most modern applications use both — TCP for authentication and account data, UDP for real-time sync and voice chat.
How GPU Servers Can Benefit Your Business
Here’s where how GPU servers can benefit your business connects directly to protocol choice.
GPU servers don’t just accelerate AI — they power the real-time data pipeline that UDP-heavy applications depend on. A live streaming platform receives video over UDP, decodes it, transcodes it into multiple resolutions, and re-delivers it to viewers — all in real time. Without premium GPU compute resources, the compute layer becomes the bottleneck, not the network.
How GPU servers can benefit your business in concrete terms: GPU-accelerated servers run real-time video compression and super-resolution for live streaming VOD platforms, handle thousands of UDP game packets per second while processing AI and physics simultaneously, and power real-time fraud detection across TCP transaction streams. Brands utilizing web hosting providers for sites with GPU-based cloud infrastructure scale with the help of traffic growth without reducing protocol performance.
Knowing about how GPU servers can benefit your business means recognizing that the compute layer and network protocol layer must work together. The quickest UDP pipeline is quite useless if all of your servers can’t easily process data quickly.
Conclusion
TCP offers complete reliability, ordering, and error revision—perfect for anything that can’t endure data loss. UDP provides raw speed and reduced latency—crucial for modern gaming, live streaming VOD platforms, and advanced communication. Neither is widely better; modern engineers generally use both where needed.
Combine that protocol knowledge with the appropriate infrastructure, especially knowing about how GPU servers can take advantage of your business, and you harness performance that hardware or software alone cannot easily match. Even if you are assessing scalable cloud hosting solutions, premium GPU compute resources, or simply developing faster apps, the protocol layer is where performance starts.
FAQs
TCP is basically a connection-based protocol that guarantees trustworthy order and complete delivery of all data, which makes it a perfect option, especially for email, web browsing, and file transfers. UDP is completely connectionless and gives priority to speed over reliability, making it perfect for gaming, live streaming, and real-time communication.
Yes. UDP has drastically lower overhead just because it skips all the connection handshake, responses, and retransmission processes.
For TCP vs UDP, especially for live streaming, UDP is an ideal option for live broadcasts because it reduces latency. A dropped frame is far less disruptive than buffering. Moreover, different on-demand video platforms (such as Netflix and YouTube) utilize TCP just because buffering makes a smooth delivery. Today’s protocols, such as QUIC (HTTP/3), are combining both tactics.
Knowing about how GPU servers can advantage your brand in this case is important: UDP-powered apps such as modern games and live streaming VOD platforms generate a huge amount of real-time tasks, such as video transcoding, complex simulations, and AI processing. Premium GPU compute resources easily manage all these compute-heavy workloads at wire speed, guaranteeing that the server keeps up with incoming UDP data streams without adding latency.
Yes, and most of today’s apps really do. A multiplayer game might utilize UDP just for real-time player movement and TCP, especially for login, purchases, and saving sensitive data. A video conferencing application utilizes UDP for audio/video and TCP for chat messages and file sharing. Selecting reliable cloud hosting solutions that support both types of protocols with reduced latency networking is important for all these hybrid architectures.