Budget-Friendly Hosting Solutions: Affordable Options That Deliver
In today’s digital age, when you start a new business or launch an e-commerce site, it is important to find a reliable web hosting service that offers you the best web hosting solution. However, finding the best web hosting provider that fits your budget without compromising on performance can be a complicated task. Website hosting is a very high-cost service, but there are various budget-friendly options available as well. In this blog, we explain why we choose Budget-Friendly Hosting Solutions and highlight the best web hosting services that provide budget-friendly hosting solutions to individuals. When searching for the best web hosting provider, Infinitive Host is the best web hosting company that offers the affordable web hosting service with factors such as reliability, performance, customer support, and pricing.
Why Choose Budget-Friendly Hosting Solutions?

Budget-friendly hosting options are essential for beginners looking to build a strong online presence, characterized by their affordability, scalability, and tailored features. Choosing a budget-friendly hosting solution offers several advantages tailored to the needs of startups, small businesses, and personal projects:
- Cost-Effectiveness: These hosting solutions are designed to be economical, ensuring that individuals with limited budgets can easily access them. They provide the necessary features needed to get started online without unnecessary expenses.
- Ideal for Small Websites and Blogs: If you’re launching a new website with normal traffic expectations, budget-friendly hosting offers sufficient resources without the extra cost of advanced functionalities.
- Ease of Use: Most budget-friendly hosting providers offer user-friendly interfaces and simple setup processes, making it easy for beginners to manage their websites without technical expertise.
- Scalability: These hosting solutions are initially cost-effective, but they also offer scalability options. As your website grows and requires more resources or advanced features, you can upgrade your plan accordingly.
- Reliability and Support: Reputable, budget-friendly hosting providers ensure reliable uptime and provide basic customer support options, ensuring your website remains accessible and functional.
Types of Budget-Friendly Hosting Solutions

Whether you’re launching a personal blog or a business website, there are various web hosting solutions that offer you the web hosting solution that fits your budget. Consider the following types of budget-friendly hosting solutions and providers known for delivering reliable service:.
- Shared Hosting: Sharing hosting is one of the most cost-effective solutions that is beneficial for beginners and small businesses. It is the best web hosting service option for startup businesses. Within a shared hosting environment, your website shares server resources such as CPU, RAM, and disk space with other websites, which helps reduce costs significantly. There are some key benefits to shared hosting.
- Affordability: Plans start with low costs. Most beneficial for beginners for their startups and personal projects.
- Ease of use: Most shared hosting providers offer user-friendly control panels like cPanel or Plesk for managing your website.
- Support: Reliable shared hosting providers offer 24/7 customer support to assist with any technical issues.
- Cloud Hosting: Cloud hosting is another best hosting service option for scalability and reliability without breaking the storage. Unlike traditional hosting methods, this service operates multiple remote servers to balance the load and maximize uptime. There are various key benefits included in cloud hosting.
- Scalability: Resources can be scaled up or down according to the level of demand. The scalability option allows the websites or applications to handle spikes in traffic without performance issues.
- Reliability: With the resources spread across the multiple servers, downtime is minimized and performance is stable. Cloud hosting offers better reliability and uptime compared to traditional hosting solutions. If one server fails, then another server quickly takes its place and minimizes the downtime.
- Flexibility: Users select the specific configurations, operating systems, and software to meet their needs.
- Cost Efficiency: Cloud Hosting offers a pay-as-you-go pricing model where users only pay as they need. This can be more cost-effective for businesses that experience fluctuating traffic.
- Security: Cloud hosting providers offer security measures to protect data and applications. They offer features like firewalls, data encryption, and regular backups to enhance security.
- WordPress Hosting: WordPress hosting specifically refers to hosting services optimized for WordPress websites. It is the most popular content management system (CMS) globally, and its providers offer servers configured to enhance the performance and security of WordPress sites. There are various benefits included in WordPress hosting.
- Optimized Performance: WordPress hosting providers optimize their servers configured for WordPress to ensure faster loading times and better overall performance.
- Automatic backups: Manage the automatic updates that help to This helps keep your site secure and up-to-date without requiring manual intervention.
- Support: Managed WordPress hosting usually comes with dedicated support from experts who are knowledgeable about WordPress.
- VPS Hosting: VPS hosting provides exclusive virtual resources within a shared server environment. It is the type of hosting in which a physical server is divided into multiple virtual servers, each running independently with its own operating system (OS), resources, and allocated portion of CPU, RAM, and disk space. In a VPS environment, you have dedicated resources allocated to your website on a virtual server. There are various benefits included in this hosting.
- Root Access: Users typically have root access, which enables them to customize server settings and install applications as needed.
- Scalability: VPS hosting offers scalability by allowing users to easily upgrade or downgrade their resources as their website or application grows or experiences changes in traffic.
- Performance: VPS hosting generally provides better performance compared to shared hosting because resources are not shared among multiple users. Websites and applications hosted on a VPS tend to load faster and handle more concurrent users without slowdowns.
- Free Hosting: For those with very limited budgets, free hosting options are the best hosting solution for them. This hosting typically comes with limitations, such as ads on your site or limited storage and bandwidth.
Whether you need shared hosting, VPS hosting, Cloud Hosting or others hosting solutions, Infinitive Host is the right web hosting service that is crucial for your business’s online presence and success.
Conclusion
Selecting the right hosting provider is a critical decision that can impact your website’s performance and, ultimately, your online success. By understanding your website’s needs and comparing available options, you can find a hosting solution that meets your requirements. Infinitive Host is the best web hosting company that provides the best hosting solutions that meet your requirements within a limited budget. Whether you’re starting a new website or looking to migrate an existing one, Infinitive Host offers web hosting services with reliable and cost-effective solutions and support to help your online presence thrive.
How to Choose the Best Web Hosting Company for Your Business
In today’s digital age, a robust online presence is essential for the success of any business. Whether you are initiating a new startup or aiming to grow your current enterprise, choosing the best web hosting provider is a critical decision that can greatly influence your website’s efficiency, security, and ultimately, your financial success. Without a web hosting service, you cannot host the website on the server. Host your website on a server is mandatory for your business.
With the multiple options available, navigating the world of web hosting can be overwhelming. In this blog, we discuss how to choose the best web hosting company to fulfill your business requirements. Here’s a comprehensive guide to help you choose the best web hosting company for your business needs:
1. Understand Your Hosting Needs: Before selecting the right web hosting service it’s essential to understand your specific hosting requirements. These requirements are:
- Traffic volume: Estimate how much web traffic you expect to find a web host that can provide sufficient resources. Higher traffic may require more robust hosting solutions.
- Website type: Depends on the website category such as it is a blog or any business website.
- Special software: Do you need specific software or applications supported by the hosting provider?
- Future scalability: Will your hosting needs grow over time?
- Budget. Set a budget and cost limitation for hosting services. Some web hosting costs more than others, so creating a budget can help organize your long-term spending.
- Platform: Find the website hosting platform which provides you the best web hosting service. Provide Proper guidance about the web hosting process
2. Types of Hosting: There are the various best web hosting provider services that is required to host a website and fulfill all the business requirements:
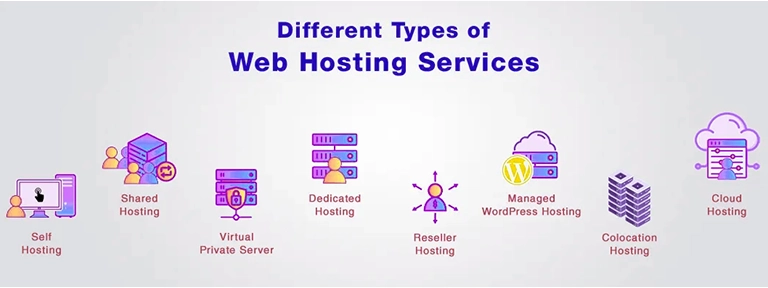
- Shared Hosting: Shared Hosting is affordable and suitable hosting for the small website with low to moderate traffic.
- VPS Hosting: VPS Hosting is ideal for growing multiple websites. It offers more access and resources than shared hosting.
- Dedicated Server Hosting: Dedicated hosting provides the full access for the high traffic.
- Cloud Hosting: Cloud hosting is Scalable and flexible. It is ideal for websites with fluctuating traffic and uses multiple servers to host a website.
3. Uptime and Reliability: Website downtime lost his rank on the search engine and negative user experience. Choosing the best hosting provider is essential, as they guarantee high uptime (99.9% or higher) and have a reputation for reliability. They ensure that your website is accessible to visitors without significant downtime.
4. Security Features: Website hosting provides the essential security features including SSL certificates for encrypting data transmissions, regular backups to protect against data loss, firewalls, and malware scanning and removal tools.
5. Performance and Speed: Fast-loading websites enhance user experience and improve SEO rankings. There are various factors affecting the performance and speed including SSD storage, Content Delivery Network (CDN) integration, and server location options.
6. Support Quality: Our expert team is always ready to resolve your queries. We offer 24/7 support through multiple channels (phone, live chat, email). We are available to answer your questions, get you started, and expand your online presence.
7. Scalability: Choose the right website hosting plan allows you easy scalability, whether through upgrades to higher-tier plans or additional services. Scalable web hosting solutions allow you to easily upgrade resources as your traffic and business expand.
8. Price and Value: Offers the best cost-effective web hosting plans to the individuals.Consider value as a priority over selecting the cheapest option, despite cost being an important factor. Compare pricing plans based on features offered, such as storage, bandwidth, and included services (e.g., domain registration, email hosting).
9. Reputation and Reviews: Research about the best web hosting provider. Read reviews and testimonials from current and past customers and be careful about customer service, uptime, and overall satisfaction.
10. Additional Features: Consider additional features such as website builders, email hosting, domain registration, and e-commerce capabilities offered by the best web hosting provider.
Why do we use the Best Web hosting Service?

As we discuss in the above section, it is crucial that hosting your website on the server. We give a brief concise overview of web hosting services. Web hosting is known as the service that enables individuals or organizations to access their websites via the World Wide Web. Web hosting providers allocate space on the servers, which are owned by the clients, and they offer various types of hosting plans that fulfill the business needs of an individual. Whether you’re looking for shared hosting, VPS hosting, or dedicated server hosting, you can select the right web hosting company that is suitable for your business needs.
Conclusion
Choosing the best web hosting company involves evaluating your specific needs against factors like reliability, performance, security, support, scalability, and pricing. According to your website needs, researching and comparing hosting providers, checking technology and features, finding dedicated support, and selecting the right web hosting service, you can make an informed decision. As a best web hosting service, Infinitive Host is the best hosting provider that fulfills all the business requirements.
Vtiger vs. Salesforce: A Comparative Analysis
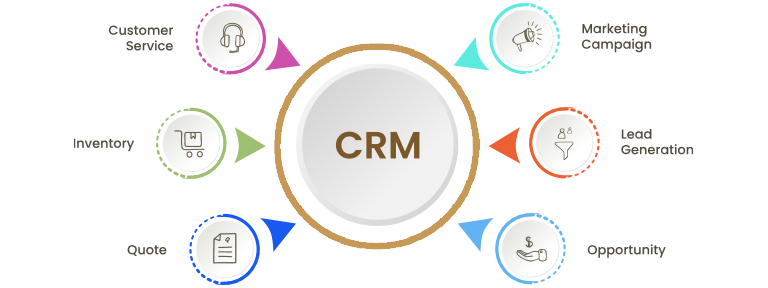
Vtiger helps to set up customer needs, the sales process, marketing needs, and support services. It is a customer relationship management software that helps manage business needs. Vtiger Hosting Software covers all the technical issues, including trouble-free migration and performance optimizations. It is the most reliable and trustworthy CRM software that helps fulfill business operations. Salesforce is a cloud-based CRM solution that is mainly focused on sales, customer service, marketing automation, analytics, and application development that increase the customer relationship and streamline the business process. Salesforce is an easy-to-learn platform. Salesforce is different from other CRM processes, and it has the ability to support small and large enterprises. It provides a high level of customization. Compare and choose between Vtiger and Salesforce, and identifying who’s the best is very difficult. Both platforms offer the best services and features. Here we explain the features and differences between Vtiger and Salesforce.
Comparing Vtiger CRM with Salesforce.

Vtiger
- Overview: Open-source CRM is the focus of SMEs and enterprises and offers cloud-based and on-premises services.
- Features: Sales Automation, Customer Support, Marketing, Customization, Inventory Management, Reports, and Analytics
- Ease of Use: User-Friendly, Quick Setup
- Pricing: More affordable, on-premises version available
- Customization and Integration: Highly customizable and supporting third-party applications
Salesforce
- Overview: Cloud-Based CRM Solutions, known for third-party application enterprises, offers a comprehensive suite of applications for sales, service, marketing, etc.
- Features: Sales Cloud, Service Cloud, Marketing Cloud, Community Cloud, Customization
- Ease of Use: Requires more technical knowledge and provides comprehensive training resources.
- Pricing: More Expensive, Offers a Wide Range of Plans
- Customization and Integration: API Support, App Exchange Services
Pros and cons of each platform for different business scenarios.

Vtiger is the best choice for small to mid-sized businesses and startups that depend on the affordability, ease of use, and suitability of businesses that require customization and have limited budgets. On the other side, Salesforce is especially beneficial for businesses that require robust integrations, industry-specific solutions, and comprehensive support. There are the various pros and cons of Vtiger and Salesforce that explain which service is best.
Vtiger:
Vtiger Pros:
- Affordable Pricing: Vtiger offers a very low pricing structure as compared to other CRM solutions. It makes it accessible to small and midsize businesses.
- Open Source: Vtiger is open source. It offers benefits for startups and small businesses with limited budgets.
- User-Friendly: Vtiger CRM has an easy-to-use interface, and it is designed to be user-friendly. It enables users to get full access with minimal training.
- Comprehensive Features: Vtiger combines sales, marketing, and customer support features into a single platform. It offers the best services, including sales automation, customer support, marketing automation, and project management. .
- Customization: Vtiger customizes all the fields, modules, and workflows to tailor the CRM to fulfill their specific needs.
- Integration: Vtiger supports third-party applications such as Mailchimp, QuickBooks, and Google Workspace to enhance its functionality.
Vtiger Cons:
- Limited Advanced Features: Fewer features and scalability options are found in the more comprehensive Vtiger CRM.
- Smaller Ecosystem: Less third-party integrations and extensions in comparison to larger CRM platforms.
- Scalability Limitations: Vtiger is a CRM solution that is scalable. It offers small to midsized businesses, so it may not be scalable for large enterprises with complex needs and high volumes of data.
Salesforce:
Salesforce Pros:
- Comprehensive CRM: Salesforce offers complete customer relationship management and powerful customization. It is the best platform to track interactions, sales, and marketing.
- Scalable and Flexible: Salesforce customizes all the specific business needs and adapts to businesses of all sizes.
- Cloud-based: Provide access anywhere with automatic updates and high security standards.
- Extensive AppExchange: The Salesforce platform provides a marketplace with pre-built apps, integrations, and industry-specific solutions.
- Automation and Workflow: The Salesforce team can automate tasks, standardize processes, and boost efficiency for your team.
- Real-time Analytics: Follow the real-time analytics process in which the user checks the insights reported into sales, marketing, and customer behavior instantly.
- Mobile Accessibility: Salesforce collaborates on iOS and Android devices and manages customer interactions.
- Integration Capabilities: Salesforce integrates with other business systems for data synchronization.
- Ongoing Innovation and Support: Support all users by using the options, including dedicated account managers, 24/7 support, and extensive training resources.
Salesforce Cons:
- Steep learning curve: Salesforce may require comprehensive training for users to become proficient in navigating
- Cost implications: Salesforce is most expensive in price, especially for larger organizations or those who need extensive customization. If you select additional features, integrations, or storage space, you need to pay the extra amount.
- Limited mobile app functionality: Users have complained about the limitations of the Salesforce mobile app. Features and customization options are not available on mobile devices and are only available on desktop devices.
- Data storage limitations: There are limitations and restrictions on data access and storage. As a result, companies are required to buy additional storage space.
- Dependency on internet connectivity: Salesforce operates primarily as a cloud-based platform, which means there is unstable internet connectivity. In these situations, users face various difficulties.
- Customization complexity: complex setup and maintenance, often requiring dedicated administrators or consultants.
Is Vtiger CRM beneficial for your business?

Yes, it is 100% true that Vtiger CRM is beneficial for your business. Vtiger is an open-source CRM, and it is the world’s leading CRM with over 5 million downloads. Vtiger CRM is the best tool because it has all the essential features that are always beneficial for any kind of business. It is cost-effective and affordable as compared to other CRMs, and it is an open-source CRM. Vtiger CRM is a customizable CRM, which is very helpful in maintaining strong relationships between an organization and its customers. Vtiger CRM’s main motive is to fulfill all business needs and provide support for any kind of issue. It helps to monitor customer details, track sales opportunities, and monitor deal status. Vtiger CRM is the game-changer. The best features of Vtiger CRM are sales automation and email marketing options. Vtiger CRM is an affordable tool that reduces marketing costs. Vtiger CRM is safe and secure. This software includes webapps, APIs, mobile apps, and IMAP/POP/SMTP email client access.
Conclusion
In conclusion, both Salesforce Sales Cloud and Vtiger CRM have their various strengths and weaknesses. Both decisions depend upon the business’s requirements and preferences, as well as the importance of pros and cons for each CRM system. Vtiger is a customer relationship management software. It is always available as both a cloud-based and on-premise solution. It varies in size and flexibility of the business. It is known as a cloud-based CRM solution that is used in project management, inventory management, process automation, and other tools. On the other hand, Salesforce is better suited for larger organizations or businesses. It has the best feature set, scalability, and powerful customization. They make it a robust choice for enterprises that need a comprehensive CRM platform with advanced capabilities. It provides a high level of customization. It is easy to learn and understand. Selection between Vtiger and Salesforce totally depends on specific business requirements, budgets, and the scale of CRM functionalities you need.
Read More : Top Vtiger CRM Features for Small and Medium Enterprises
Top Vtiger CRM Features for Small and Medium Enterprises
Vtiger CRM is a particularly good match for small and medium enterprises due to its affordability, ease of use, and comprehensive feature set. It offers a wide array of features that align business operations and fulfill all the requirements of small and medium enterprises across sales, marketing, and support teams. Customer relationship management software is best for small and medium enterprises and is available at places like SugarCRM and Salesforce.com. Vtiger CRM offers you the ability to focus on the customers and resolve their service-related queries. Vtiger CRM offers the Small and Medium Enterprises feature designed for sales, marketing, and support teams. Small businesses benefit from implementing the CRM solution with improved customer interactions, improved sales performance, centralized data management, and targeted marketing campaigns. It empowers us to build strong relationships with our customers and provide support when they need any type of support. Here we define the Vtiger CRM features for small and medium enterprises.
- Leads Management: Vtiger CRM manages the leads and converts them for better opportunities. It has the ability to import leads from external sources such as webmail, seminars, and email. After collecting all the leads, users convert their leads into sales opportunities with just one click. You can import all the leads with all these resources in bulk. It saves you time and effort. It is helpful for the sales team to manage the records instantly.
- Product Customization and Inventory Management: It manages the product list according to business requirements. It also gives the option of drag-and-drop to shortlist the products. Products also represent God’s stock in the inventory. It can be either acquired from your suppliers or rendered to your customers. The product module acts as a bridge between the sales and purchase departments; it happens when the company both sells and purchases goods.
- Enhanced Customer Relationships: Vtiger CRM allows small and medium enterprises to maintain customer engagement by providing purchase histories and communication patterns.
- Managing Customer Support: Manage the self-service support and customer support tickets efficiently. Track the ticket status and its priority. Tickets are provided to handle the cases. You need to create a case for a product.
- Customization: Customizing the CRM is one of the most important benefits of Vital CRM. As Vital CRM is open source, it can be customized as per the company’s requirements. Modify your Vtiger CRM service as per your business flow.
- Managing other activities: Vtiger CRM manages regular and daily activities that can help conduct the sales process. To secure the activity in the future, Vtiger CRM maintains all the email marketing activities that are related to the customers.
- Managing Sales Orders and Invoices: After the purchase order is received, a sales order is generated by the company. It can be converted into an invoice, which saves you time and effort. It helps the sales team track all the products and services according to their details, dates, and times.
- Workflow Automation: Automation processes reduce the valuable time of customers, such as follow-ups, emails, and lead nurturing.
- Real-time Reports: Vtiger CRM reveals all the performance indicators, forecasts, and future trends by checking the insight reports.
- Contact Management: Track the customer details and contact them across multiple channels, such as calls, email, chat, and social media.
Real-world examples of how SMEs are leveraging Vtiger.
Vtiger CRM software has the ability to track real-time customer information. After tracking the information, it identifies the issue in the software, so they provide support to the customer. Small and medium enterprises work in the real world to make direct contact with anyone and give them support instantly. There are some real-world examples of SMEs leveraging Vtiger CRM to improve business growth.
- Digital Marketing Agency: Streamlining Lead Management and Campaign Tracking: A digital marketing agency is mainly focused on SEO, PPC, and social media advertising. The agency needs an efficient way to track client communications, generate leads, and measure the usefulness of the marketing campaign. Vtiger CRM captures the automatic leads from the website and various social media channels. Maintain the client records, run the email marketing campaign, generate a report of the marketing performance of the campaigns, analyze it, and maintain the custom report. Check the insights and manage the marketing performance data.
- Manufacturing Company: Optimising Sales Pipeline and Inventory Management: A small manufacturing company needs to optimize its sales pipeline and inventory management. Visualize and manage the sales pipeline, and maintain a record of the inventory to ensure timely delivery and production. Automate reminders and time-to-time follow-up for the sales team and ensure a timely response from the customer side.
- IT Service Firm: Enhance Customer Support and Project Management: IT Service manages the project management process and customer support tickets. It improved customer support efficiency and project management. Give a timely resolution to the customer’s issue. This process works on the project management process to plan, execute, monitor the various tasks, and track progress.
- E-commerce Retailer: Integrating Sales and Customer Data: Works for customer data and integrated sales. Synchronize the customer order data from the e-commerce platform to Vtiger CRM. Managers send follow-up emails, thank-you notes, and promotional offers based on customer behavior.
- Consulting Firm: Automating Client Communications and Reporting: The consulting firm works on business strategy and financial services. They manage the client report and communicate with them. Keep track of the project management, generate custom reports on financial metrics and project progress, and automate email communication for newsletters and follow-up reminders.
How does Vtiger CRM work?
Vtiger CRM is an open-source architecture that allows for the management of reporting, information databases, campaign management, lead management, care studies, and inventory management. In addition, the Vtiger CRM is developed on highly reliable technologies such as Apache, PHP, Linux/Windows, and MySQL. Vtiger CRM tracks all the sales opportunities and manages the technology to improve their rank in the market. They are responsible for managing the efficiency of the CRM data and software to resolve customer issues. Vtiger CRM especially works on the customer relationship management feature, which means supporting their customers timely. It is a good job for you if you dedicate yourself to helping your customers and making a positive impact. You can resolve customer issues related to business operations and other needs. One of the best features of Vtiger CRM is that it supports internal processes and allows employees of the business to manage the data in a better way.
Conclusion
The real-world examples of Vtiger SMEs highlight how SMEs support Vtiger CRM to streamline business operations, improve customer relationships, and drive business growth. By utilizing their features, they can manage leads, automate tasks, enhance customer support, and gain valuable insights through reporting and analytics. As a result, these processes achieve better business outcomes. Vtiger CRM works on various CRM functions such as marketing automation, service functions, sales automation, and customer support. It provides a flexible and affordable solution that fulfills the needs of SMEs. They meet all the requirements of small and medium enterprises. The most important feature is that SME can align their business growth, sales, marketing, and customer support processes and improve the efficiency of the business. Vtiger CRM helps SMEs align their business goals in a more effective manner.
Read More : Vtiger vs. Salesforce: A Comparative Analysis
Customizing Vtiger CRM: Best Practices and Tips
Vtiger CRM is a customizable platform. There are various settings that you can customize, such as custom fields, roles, profiles, workflow rules, approval rules, assignment rules, business hours, email settings, user groups, authentication methods, picklist values, phone settings, SMS settings, field labels, currencies, and taxes. Vtiger CRM is an open-source software used by small and medium enterprises. It is used to manage inventory management activities such as sales force automation, customer care and service, marketing automation, procurement, and fulfillment. Customizing Vtiger CRM effectively involves understanding the platform’s capabilities and customizing the options. Our Vtiger CRM developers are fully experts in CRM solutions as well as business modules. Not only is it one of the most important features of the CRM market, but it is also the most trustworthy and affordable in price. It offers free as well as the most affordable price plans in the market. Multiple CRM systems allow you to customize the workflows that fit the business’s needs. There are best practices and tips for customizing Vtiger CRM. By following these business tips, you can effectively customize the Vtiger CRM for your business purposes and boost your overall productivity.
- Understand Your Business Needs: Before customizing Vtiger CRM, you need to understand your business processes to understand what needs to be customized. Set up the goal and objectives, such as improving workflow efficiency or enhancing data management.
- Built-in Customization Options: Vtiger CRM allows you to add custom fields to capture additional data that is relevant for your business. Set up the workflows to automate email and report generation. Modify the layout and create custom modules to manage the business process.
- Integrate Third-Party Apps: Vtiger integrated third-party apps such as email marketing platforms, accounting software, and more. Enhance the CRM functionality and provide the Vtiger Marketplace for extensions.
- Leverage Customization Services: Customize the Vtiger CRM to stay up-to-date with the latest releases and patches. Regularly monitor the CRM software’s performance.
- Custom Coding: Use the scripts and code snippets for advanced functionalities. It utilizes the Vtiger API to integrate with other systems or to build custom features.
- User Roles and Permissions: Define roles and permissions to control access to various parts of the CRM. Also, create the profiles for the different user roles effectively.
- Testing and Feedback: Use a sandbox environment to test customizations before deploying them to production and collect feedback from users to identify areas for improvement.
- Training and documentation: Provide the user with proper training on how to use the custom features.
- Security and Compliance: Vtiger CRM ensures that customizations comply with relevant industry standards and regulations. They implement security measures to protect sensitive data.
- Update regularly about the latest versions: Stay updated about the latest version of the CRM, new releases, and updates to ensure that the customizations remain compatible and fully functional.
Guide to tailoring Vtiger CRM to meet specific business needs
Vtiger CRM offers customization options to align the business platform with specific business requirements. Tailoring Vtiger CRM to meet the specific business needs involved in the customization and configuration process. Here we describe the comprehensive guide to tailoring Vtiger CRM that helps you through the process.
- Access business processes and requirements: Analyze the business areas for improvement and automation. Identify areas where Vtiger CRM can streamline operations, improve efficiency, and enhance customer relationship management. Understand what you want to achieve with CRM, such as improved sales tracking and enhanced customer service.
- Utilize Custom Fields and Layouts: Develop custom fields and customization layouts that are relevant to your business. include customer-specific information, product details, or industry-specific data. Tailor the layout of the records to display the most relevant information in a prominent way.
- Configure Workflows and Automation: Setup the workflow rules to automate routine tasks such as sending notifications or updating records. Set conditions and actions for the workflow based on the specific criteria. Schedule daily routine data and maintain the tasks.
- Integrate the Third Party Applications and Marketing Extensions: Integrate the Vtiger Third Party Applications such as email marketing platforms, accounting software, and communication tools. Explore the Vtiger Marketing pre-build extensions that add functionality.
- User roles and permissions: Manage data security and compliance. Play an important role in controlling access in the different parts of the CRM.
- Data Management: Implement validation rules to maintain the integrity of the data. Utilize all the import and export tools to manage bulk data efficiently. Remove the duplication in the data.
- Training and Support: Provide comprehensive training to the user and train them about how to customize the Vtiger CRM. Maintain documentation of all consumptions for future reference. Set up the support system to resolve customer queries.
Tips on Using Vtiger’s Customization Options Effectively

Vtiger CRM provides strong customization options that can significantly enhance business operations and functionality. It has a customization option to tailor the platform to your specific business needs. Vtiger CRM is a powerful platform that makes your business unique every time. To maintain growth in your business, you need custom solutions that work for you. With the help of customization, you can improve all the processes and complete all the specific needs. Vtiger customization integrates your CRM software with your systems. They complete the full integration process in very little time. The Vtiger customization process is better than other processes. There are some tips that help customize the CRM software.
- Prioritize Custom Fields and Layouts: Identify the unique data before adding it to the custom fields. It used appropriate field types such as ext, number, date, picklist, etc. to check the accuracy and consistency of the data. Customize all the mandatory fields and record layouts to ensure that the mandatory data and information are displayed for easy access and management.
- Understand Your Business Requirements: Define your business needs and requirements to identify the specific areas that need customization within Vtiger CRM.
- Workflows and Automation: Repetitive tasks and processes can be automated within Vtiger CRM to improve operational efficiency. Configure the workflow instruction to automate lead assignment, email notifications, and other routine tasks.
- Seamless Integration with External Systems: Utilize the Vtiger CRM integration capabilities in order to connect with third-party applications. Identify the external applications and systems that can be integrated with the Vtiger CRM process.
- Regular Updates and Maintenance: Take regular backups to prevent any type of data loss. Update the Vtiger features with the latest version and security. Monitor the overall performance of the CRM to ensure that it runs in a smooth and efficient manner.
Conclusion
Vtiger CRM offers tools that can make you successful in today’s competitive market. It is a powerful tool that enhances the efficiency and effectiveness of SMEs. Vtiger CRM has various customization options and integration capabilities that can improve business efficiency, sales, marketing, customer support, and overall operational efficiency. Vtiger CRM is known as a comprehensive, flexible, and affordable customer relationship management solution that is tailored to meet the requirements of SMEs. In conclusion, we can only say that Vtiger CRM maintains its value for small and medium enterprises that aim to streamline their operations, enhance customer relationships, and drive sustainable growth.
Read More : An Introduction to Vtiger: Everything You Need to Know
An Introduction to Vtiger: Everything You Need to Know
Vtiger is a customer relationship management software that helps manage business needs. It helps to set up customer needs, the sales process, marketing needs, and support services. This process helps to improve the business’s efficiency and enhance its performance by providing various functions and tools, such as sales, help desks, and marketing teams. It is always available as both a cloud-based and on-premise solution. It varies in size and flexibility of the business. It is known as a cloud-based CRM solution that is used in project management, inventory management, process automation, and other tools. It is free for open-source software. It helps to monitor the situation and opportunities. This CRM software offers their clients a platform that increases their business productivity. Our Vtiger Hosting Software covers all the technical issues, including trouble-free migration and performance optimizations. It is the most reliable and trustworthy CRM software that helps fulfill business operations.
Overview of Vtiger CRM and its key features

Vtiger is a powerful customer relationship management tool that helps align the business in the sales, marketing, and customer service processes. This CRM platform allows all departments to collaborate in their work and support their customers according to their business needs. It is a CRM tool that provides a wide range of functionalities to streamline operations and boost performance across sales, automation, and management. There are various numbers of key features that work for Vtiger CRM Services:
- Sales Automation: It manages and tracks the overall sales opportunities, tracks potential leads and assigns them to the sales representative, and monitors progress through the sales pipelines. Generate the quotes, invoices, and orders directly within CRM.
- Customer Support: In this key feature, Vtiger manages service level agreements to ensure high-quality customer service. They resolve customer queries, manage their support tickets, track their status, and resolve their issues timely.
- Market Automation: It manages the overall marketing automation platform, in which marketing, social media marketing, campaign management, and lead nurturing are included. They plan, execute, and track the marketing campaign through the various channels.
- Project Management: They plan and manage the project timelines. Facilitate team collaboration with all the file attachments and create, assign, and check their progress.
- Inventory Management: Manage the product information with all the details. Maintain the vendor information, their purchase record, track stock movements, and manage the reorder points.
- Customization: Maintain the custom reports and dashboard to evoke business insights and key metrics.
- Integrations: Integrate the Vtiger to connect with other software and build integrations with third-party applications such as email clients, accounting software, and e-commerce platforms.
- Reporting and Analytics: Generate real-time reports on sales performance, customer interactions, and marketing campaigns. Use the advanced analytics to gain insights into business performance and customer behaviour.
- Mobile Access: Enables users to stay connected with their team and access their data with the Vtiger Mobile app, which is available in both Android and iOS versions. It also works offline when you are back online.
- Security and Compliance: Confirm the data security with encryption, backups, and robust access controls. Follow and adhere to industry standards and regulations with Vtiger’s compliance features.
Benefits of using Vtiger for business operations

Vtiger CRM is one of the most powerful tools because it provides multiple benefits for businesses to boost their operations. Here are some of the key advantages of Vtiger CRM business operations.
- Centralized Data Management: Vitger merges all the customer information into a single, centralized database. It provides a centralized platform for managing customer data, sales processes, marketing campaigns, and customer support. With an extensive customer profile, businesses can view all the purchase history, support tickets, interactions, and other essential data in one place, which enables more effective customer interactions.
- Improved Sales Efficiency: It consists of automating repetitive sales tasks such as automation tools, including lead management and opportunity tracking, to help sales teams manage and prioritize leads, which can improve conversion rates and sales performance. Automated sales tasks such as follow-up reminders and data entry help the sales team focus on high-value activities. Uses pipeline management tools that help sales teams track opportunities, identify bottlenecks, and prioritize efforts to close deals quickly.
- Boost the Customer Support: The Vtiger Helpdesk helps to manage the manager’s customer support tickets efficiently and resolve the issue timely, which improves customer feedback.
- Data-driven insights: As you studied earlier, customer feedback and satisfaction record the data. It generates powerful insights that track sales opportunities in the future.
- Better work efficiency: With daily routine task automation, the CRM tools elevate work efficiency so they can improve it in the future.
- Faster decision-making: The data analytics tools and insights help business owners make decisions faster.
- Increased revenue: Vtiger CRM accurately records the profit. It points out accurate insights and points out the revenue report.
- Quality customer service: Vtiger CRM has a clean track record of the customer, so it is easy to find out their queries. Customer retention and brand elevation are the most important benefits of the Vtiger CRM.
Is Vtiger a good CRM? Which CRM is most used.

Yes, this statement is correct. Vtiger is a good CRM. In other words, we can say that Vtiger CRM is a game changer. Vtiger is the world’s No. 1 open source project, with over 5 million downloads. It is considered a good CRM for multiple businesses, especially small and medium enterprises. The best features of the Vtiger CRM are sales automation and email marketing. These features help to increase productivity. It is most affordable in cost and reliable in terms of services. Now it is important to know which CRM is used the most often. Salesforce is one of the most essential CRM programs, and it is the top-ranked CRM software today. It is very easy to customize this CRM software and upgrade if there are any changes. It is suitable for large enterprises.
Conclusion
Vtiger CRM offers a wide range of benefits that can significantly increase business operations, improve business efficiency, and drive growth. It is a flexible, robust, and affordable solution to fulfill the needs of SMEs. It offers business operations in which sales, marketing, and customer support processes are included. Vtiger CRM can meet the needs of any SME and make it a valuable tool for enhancing business efficiency and productivity. However, it is important to complete or access your business goals, figure out the CRM capabilities, and check all its objectives on a trial basis.
Read More : Customizing Vtiger CRM: Best Practices and Tips
Customizing Odoo: Tips and Tricks for Personalising Your ERP
Odoo Customization refers to customizing the business and tailoring its needs. The appearance of the Odoo ERP software matches your specific business requirements. With the customization process, you can modify all the existing modules that fulfills all your business requirements. When it comes to customizing, Odoo has a number of benefits that enable it to enhance your business operations. They have various benefits, including enhanced efficiency, improved user experience, scalability, and flexibility in workflow. Here are some tips and tricks for customizing Odoo and personalising your Odoo instance.
- Use the Studio App for Customizations: Odoo ERP is a powerful tool that enables you to customize your Odoo applications without any coding process. By using these tips, you can create new fields, automate workflows, and design new applications. Automate the business process and use a drag-and-drop interface.
- Custom Modules: Set up a module structure including various modules and a Odoo development environment using Odoo.sh or a local setup with tools like Docker.
- Custom Views: In this module, XML Views play an important role that enables you to change the layout, add new fields, or modify existing ones.
- Automated Actions and Server Actions: Set up automated actions to perform specific tasks, like sending an email when a sale order is confirmed. Another one is server actions that execute the custom server-side logic, such as updating records.
- Advanced Security and Access Control: With this customization process, you can read, write, create, or delete records in different models and set up groups and records based on the conditions.
- Custom Fields and Models: Add custom fields to capture the additional data and use model inheritance without any core code that must be specific to your business needs.
- Integrations: Integrate the Odoo Module through the API interface and third-party applications to add new functionality.
- Multi-Company Setup: Odoo supports multi-company setups that manage multiple companies and automate transactions for sales and purchases of services or products.
- Localization: Configure the taxes, accounting, and other financial terms. Add multiple languages and translate fields, reports, and templates.
- Performance Optimization: Odoo ERP optimize performance by adding indexes to query fields. Improve the performance by using caching mechanisms.
- Testing and Debugging: Testing all the custom modules to ensure they are correct or not. Use debugging tools to resolve the troubleshooting problems.
- Training and Documentation: Conduct the training sessions to be aware of the customized features. Maintain the documentation for the customization process so new users can easily understand it.
Guide to customizing Odoo to fit specific business needs.
Odoo customizes the business, tailoring it to fulfill all the business requirements. Here are the following steps that will help you learn how to customize Odoo for your business.
- Understand Your Business Requirements: These steps understand the business requirements and fulfills all the needs that users want to run their business. Before moving into customization, you clearly understand the business process and want to know how CRM supports it. There are various aspects of the business, like sales, CRM, customer support, marketing campaigns, inventory, accounting, HR, project management, etc.
- Set Up the Basic Configuration: Download and install Odoo from the official website, follow the initial setup, and configure all the information.
- Customize Modules: Install the modules that align the business process and customize each module by enabling their features.
- Customize Fields and Views: Modify the layout and add the custom field to capture the specific data as per the requirement.
- Automate Workflows: Set up automated tasks like sending emails, updating records, or creating tasks, and use the server actions.
- Integrate Third-Party Applications: Use API software to integrate other software applications and install third-party applications.
- Customize User Experience: Create roles, dashboard, and access the rights for the different user roles.
- Enhance Customer Interaction: Customize the email templates and set up the customer portal that enables clients to access their information.
- Reporting and Analytics: Customize the report and export the data in the csv or external format.
- Data Management: Implement validation rules to maintain the integrity of the data. Utilize all the import and export tools to manage bulk data efficiently. Remove the duplication in the data.
- Training and Support: Provide comprehensive training to the user and train them about how to customize the Odoo ERP. Maintain documentation of all consumptions for future reference. Set up the support system to resolve customer queries.
- Continuous Improvement: Feedback is an important tool to improve performance. We need customer feedback so we can improve the customized services.
Tips on using Odoo Studio and Custom development.

Odoo Studio and Custom development enables you to tailor your business needs or requirements. In Odoo Studio, the companies manage the multiple numbers of companies on the single platform but on Odoo Studio, customization is done through the API or developments. Odoo studio is used for customizing your applications and odoo studio, there is no coding needed. There are various tips used in the Odoo Studio and custom development.
1. Tips on using Odoo Studio
- Activate Odoo Studio: Click the Studio icon and drag and drop to select the option. After following the steps, the Odoo Studio is activated.
- Customize Fields and Views: Add and modify the new fields into the form and then rearrange it to optimize it for your business processes.
- Create Custom Applications: Create new databases and applications to store data specific to your business.
- Automate Workflows: Automated the emails and set up the records of the user groups.
- Reports and Dashboards: Design the dashboard and custom reports by adding the KPI option that is suitable for your business.
- Testing and Publishing: Preview your work before publishing and change if there is any error.
2.Tips for Custom Development
- Set Up a Development Environment: Setup the Integrated Development Environment by using the virtual machine.
- Understand the Odoo Framework: Learn the module structure of Odoo and train yourself with all the modules and features of the Odoo Modules.
- Develop Custom Modules: Develop the new and existing Odoo modules to extend Odoo’s functionality.
- Customize Views with XML: Add a button to arrange fields and elements in XML Views.
- Security and Access Control: Implement records and define ACL to manage all the records.
- Testing and Debugging: Preview your work before publishing and correct it if there is any error.
- Deployment and Maintenance: Regularly update your custom modules and use GIT version control to manage your custom modules.
Conclusion
Odoo ERP gives you the best advantages for your business in terms of scalability, integrity, and cost-effectiveness. Odoo is a powerful tool that helps to improve your business efficiency, reduce costs, and maintain customer satisfaction. With the correct strategy and plans, businesses can grow in the competitive market and earn the highest rank. They integrate the various business processes into a single platform, which helps you improve workflow efficiency and decision-making, streamline operations, and increase your business productivity.
Read More : Top 10 Odoo Modules for Small Businesses
Top 10 Odoo Modules for Small Businesses
Odoo is a powerful tool that fulfills all the users business needs. It is a comprehensive suite of business applications that align the needs of small to large businesses. Odoo modules ensure data flows seamlessly across different departments. It provides a facility for small businesses to manage their operations efficiently. Odoo Modules provides the top 10 business module applications, such as CRM, e-commerce, accounting, inventory, POS, project management, and MRP. Odoo has become the best choice for many businesses because it meets all the requirements of the users who want to start their business. It is a complete suite of all business needs and open-source software. These modules are also useful for small businesses. Odoo is a powerful tool that helps to improve your business efficiency, reduce costs, and maintain customer satisfaction.
Highlighting the most useful Odoo modules for small business operations.

In this blog, we explain the most useful Odoo modules for small businesses.
- Sales: Create and send the sales order. Manage discounts and prices. After you confirm the order, generate the invoice and bills.
- Inventory: Track the warehouse location and stock level. Automated inventory valuation to maintain accurate accounting.
- Purchase: Manage Purchase Order and Supplier Information. Automation of procurement with rules and productivity.
- CRM (Customer Relationship Management): Manage and visualize the leads and sales pipeline. Track and schedule the customer meetings and calls.
- Accounting: Maintain all the financial accounting reports, vendor invoices, and bank statements with full records, and manage the account chart.
- HR: Manage all the recruitment, leave, and full employee records.
- Project Management: Create and assign the tasks and set the deadlines. Plan and schedule the projects and their deadlines. Track the progress of tasks and their duration.
- Website E-Commerce: Optimize the website for search engines and manage the website with a drag-and-drop editor.
- Marketing: Manage the social media channels and run the email campaigns. Automate all the marketing campaigns.
In addition to all these features, Odoo ERP works on modules such as Helpdesk, Point of Sale, Expenses, Payment Gateways, and other business tools.
Another Important Terms in Odoo Software
Odoo ERP is a comprehensive business management software. Odoo has various terms. By understanding these terms, you can configure the system, develop custom modules, or manage day-to-day operations. Here we explain the different Odoo terms.
- Odoo.Sh: It is the platform that is made by Odoo users. It enables end users to test developments easily and manage their own duplicates of their customers’s production instances.
- Odoo Partners: It has to access the different restricted features of Odoo for end users. They access the source code of Odoo ERP. Odoo partners are divided into categories: Gold, Silver, and Ready.
Why Choose Oodles ERP For Odoo Application Development?

Selecting the Oodles ERP for Odoo application development is most beneficial for the business needs. The Oodles ERP is the best choice for business users who want to tailor their business. Here we explain the reasons why Oodles ERP might be a good choice.
- Customization Capabilities: Oodles ERP offers deep customization options and allows business users to modify their operational needs and efficiency.
- Expertise in Odoo: Oodles ERP is an expert in developing and customizing Odoo applications, and they ensure tailored business solutions that fulfill all their requirements.
- Comprehensive Services: Oodles ERP provides end-to-end services, and they handle the entire life cycle of the Odoo ERP system from the initial to the final stage. There are various services included in this process, such as consulting, implementation, customization, integration, and support.
- Integration Expertise: Oodles ERP integrates with other business systems and third-party applications and integrates the capability to extend various systems like eCommerce platforms, payment gateways, and other enterprise applications.
- Scalability and Flexibility: It is the Scalability and Flexibility Solutions and evolves all the business requirements. They have on-premises or cloud-based business solutions.
- Cost-Effective Solutions: It provides high-quality Odoo development and customization at an affordable price. It is the most beneficial option to provide the facility to small and medium-sized businesses that look to maximize their return on investment.
- Technical Support and Maintenance: Oodles ERP offers full on-the-spot technical support and maintenance services that run the system smoothly. They update the information regularly, fix bugs, and optimize performance with their support services.
- User Training and Documentation: They complete the documentation process to ensure that users are comfortable and proficient with the system. Provide comprehensive training on the new system. Run day-to-day operations and troubleshooting processes regularly.
- Case Studies and Testimonials: Oodles ERP has been successful in various industries. Its expertise lies in positive testimonials and case studies that highlight their reliability.
- Innovation and Best Practices: Stay updated with the latest technologies in Odoo Development, innovative solutions, and incorporating best practices into their projects.
Examples of how these modules can streamline various business processes
Streamlining is a term that can act as an easy and simplest term that makes it more efficient. In this article, we explore the Odoo Modules with their examples, which tailor your business processes and improve business efficiency. Let’s explore all the Odoo business modules that can streamline the various business processes. There are the following ways to streamline business processes.
- Increased cost efficiency: Streamlined business processes save money so you can collect your funds for the future. It requires less staffing because the data entry process is completed automatically.
- Improved productivity: In this streamlined process, when they have ideas for assigning tasks and setting deadlines, Plan and schedule the projects and their deadlines. By using this strategy, productivity will improve.
- Better time management: managing time is very important. It will help you complete the process in less time. With fewer tasks, you will manage your time better and complete the most important tasks on time.
Conclusion
Odoo ERP gives you the best advantages for your business in terms of scalability, integrity, and cost-effectiveness. Odoo Hosting is a powerful tool that helps to improve your business efficiency, reduce costs, and maintain customer satisfaction. With the correct strategy and plans, businesses can grow in a competitive market and earn the highest rank. They integrate the various business processes into a single platform, which helps you improve workflow efficiency and decision-making, streamline operations, and increase your business productivity.
Read More : Getting Started with Odoo: A Beginner’s Guide
Getting Started with Odoo: A Beginner’s Guide
Odoo is an open-source business application that fulfills overall company requirements such as CRM, eCommerce, accounting, inventory, point of sale, project management, etc. It offers a wide range of features to streamline business operations. It is an open-source ERP and CRM used for business management purposes. Odoo provides integrated business apps called Odoo apps. Odoo is the business management software that integrates all the business requirements. There are various tools, including customer relationship management, e-commerce, billing, accounting, manufacturing, warehouse management, project management, and inventory management. It is the world’s easiest management software and includes more than hundreds of applications. It is a large collection of business applications and modules. These modules are known as enterprise resource planning software. Odoo starts small and scales up the business. It allows you to access the new features without interruption. It helps you in business operations by streamlining processes, improving collaboration, and boosting productivity.
Step-by-step instructions for new users to set up and navigate Odoo

Here are the steps in which we guide you through the process of Odoo, from installation to basic configuration and usage.
- Installation: Before the installation of Odoo Software, your system needs things such as OS, Python, PostgreSQL, RAM, and disk space. Follow the instructions to set up the software and configure it according to your business requirements.
- Setting up Odoo: What requirements do you have to set up your Odoo software or opt for the cloud-based solution?
- Initial Configuration: Access Odoo via your web browser at http://localhost:8069 After that, create a new database, and then login with the credentials. After that, install all the modules, such as CRM, Sales, Inventory, and Accounting.
- Basic Information: Enter the basic information at the time of installation. Go to Settings, and then update the company information.
- Configure your modules: Configure your modules like CRM, Sales, Inventory, and Accounting, and then manage the customer details record. Explore the CRM and sales modules to manage the leads. Understand how to use inventory management at different levels. Maintain records of purchasing invoices, payments, and financial reports. Also, learn about Odoo Software project management planning and collaborate with all the team members.
- Navigation Tips: Follow all the navigation details to find all the details mentioned in your records.
- Customization and Configuration: Odoo ERP is highly customizable. By using the Odoo module, you can customize the forms, views, and workflows without writing the codes. You can develop the Odoo Custom Modules by using the Odoo Applications after the installation process.
Why Implement Odoo ERP? Reasons To Choose Odoo ERP?

Odoo is an open-source application. It is an ERP system. It has user-friendly and powerful features. Odoo is a comprehensive solution to meet all the business needs of new-age enterprises. It is a significant way to integrate the functions into a single, unified system and transform the way your business operates. There are several reasons to choose the Odoo ERP System.
- Comprehensive Suite of Applications: Odoo offers different applications for your business needs, such as CRM, sales, inventory, accounting, HR, project management, manufacturing, and e-commerce.
- Modular and Scalable: Odoo’s modular architecture enables you to begin with the important applications that grow your business. It ensures that Odoo can align your business needs without requiring a complete system.
- User-Friendly Interface: Odoo’s user-friendly and modern interface makes it easy to perform tasks immediately.
- Customizability: Odoo is a highly customizable process that allows businesses to tailor the system to specific workflows and needs. With Odoo ERP System, you can modify forms, views, and workflows without any extensive programming knowledge.
- Cost-Effective: Odoo offers more cost-effective solutions. It offers the system at an affordable cost, which extends to implementation and maintenance costs.
- Integration Capabilities: Odoo integrates with third-party applications such as payment gateways, shipping carriers, communication tools, and other business applications.
- Real-Time Data and Reporting: Odoo provides real-time access to business data and enables the decision-making process. It is the tool that generates detailed reports and provides insights into various applications. It has real-time visibility, which helps you stay on top of the key performance indicators.
- Improved Customer Experience: With the help of Odoo modules, it helps you provide better customer service. You can track the customer experience, provide feedback, manage the sales pipelines, and provide timely support, which gives direction to the best customer experience.
Overview of essential features and modules

Odoo ERP is an open-source, comprehensive business management software. It integrated the various business applications into a single platform. It enables users to choose the deployment option as per their business requirements. This service is available in both on-premise and cloud-based versions. Odoo ERP provides the best customer support that optimizes the business process. The support team is available all over the world to resolve any query. Here we overview the best features and modules of the Odoo ERP System.
Features of Odoo ERP System
- Modular Architecture: Odoo enables you to install the applications and tailor your business process according to your requirements.
- User-Friendly Interface: Odoo provides a user-friendly and modern user interface. It reduces the learning curve for new users.
- Integration: Odoo integrates all the customer data consistently and improves workflow efficiency.
- Customizability: Odoo is a customizable system that caters to the business needs of its users. It can customize forms, views, and reports without any requirement for codes. The modules are developed by the users with the help of the Python and XML languages.
- Scalability: Odoo creates new modules and scalability to manage the business management software and also enables new and additional modules.
- Community and Enterprise Editions: Odoo offers an open-source, free community edition and a paid enterprise edition.
Modules of Odoo ERP System
Odoo has various numbers for the module that helps to maintain the business needs of the users. Here we explain the various Odoo ERP modules in detail.
- CRM (Customer Relationship Management): Manage and visualize the leads and sales pipeline. Track and schedule the customer meetings and calls.
- Sales: Create and send the sales order. Manage discounts and prices. After you confirm the order, generate the invoice and bills.
- Inventory: Track the warehouse location and stock level. Automated inventory valuation to maintain accurate accounting.
- Purchase: Manage Purchase Order and Supplier Information. Automation of procurement with rules and productivity.
- Accounting: Maintain all the financial accounting reports, vendor invoices, and bank statements with full records, and manage the account chart.
- HR: Manage all the recruitment, leave, and full employee records.
- Project Management: Create and assign the tasks and set the deadlines. Plan and schedule the projects and their deadlines. Track the progress of tasks and their duration.
- Website E-Commerce: optimize the website for search engines and manage the website with a drag-and-drop editor.
- Marketing: Manage the social media channels and run the email campaigns. Automate all the marketing campaigns.
In addition to all these features, Odoo ERP works on modules such as Helpdesk, Point of Sale, Expenses, Payment Gateways, and other business tools.
Conclusion
Odoo is a powerful tool that helps to improve your business efficiency, reduce costs, and maintain customer satisfaction. This guide is used to describe the full process of Odoo for beginners. After following all the steps of Odoo and navigating effectively, you can start to work on the Odoo Business Software. Starting the process from installation to initial configuration and the basic use of the Odoo function, describe how you tailored it to your business needs. Odoo ERP gives you the best advantages for your business in terms of scalability, integrity, and cost-effectiveness. They integrate the various business processes into a single platform, which helps you improve workflow efficiency and decision-making, streamline operations, and increase your business productivity. In short, we can say that Odoo ERP is the best choice for managing your business efficiently. For more details about customization and advanced usage, refer to the extensive documentation and community resources.
Read More : Top 10 Odoo Modules for Small Businesses
Comparing Leading GPU Server Providers: Which One is Right for You?
Whenever it comes to selecting a GPU Dedicated server providers, we think about which one is the best dedicated GPU server. GPU Dedicated servers are the best choice for you because they offer you the ability to increase power and maintain speed on computing devices such as video rendering, data analytics, and machine learning. GPU Dedicated servers work for AI and machine learning, which will be very useful tools in the future. GPU Dedicated servers are based on various key factors such as performance, pricing, availability, support, and specific use cases. GPU Dedicated Server is open-source and user-friendly. GPU Dedicated servers offer higher computational permanence in comparison to CPUs. In terms of the CPU, GPU servers are cheaper and offer higher performance. In addition, multiple GPU servers run on a single server. You can choose the GPU Dedicated server that understands your AI application performance requirements. NVidia is one of the best GPU dedicated servers and fastest GPU Server, which is a game changer in the field of performance and acceleration.
A detailed comparison of GPU server providers like AWS, Google Cloud, and Azure
GPU Dedicated Server are the various numbers of GPU server providers that provide the best cloud services to their users. There are the best examples of GPU server providers like Amazon Web Services, Google Cloud, Azure, and many more. Here, we compared all these GPU server providers and found which service was the best.
Amazon Web Services (AWS):

- Performance: AWS offers a comprehensive range of GPU instances, including the NVIDIA A100, V100, T4, and older models like the K80 and M60. It offers high-performance network data services.
- Pricing: AWS’s pricing varies based on standard on-demand pricing for flexibility. AWS offers Reserved Instances, which can give up to a 75% discount for long-term commitments.
- GPU Options: T4 and G4ad (Radeon Pro V520) offer a range of performance options.
- Best for: AWS Cloud Service is best for large enterprises with demanding workloads.
- Features: AWS includes a comprehensive range of services such as advanced analytics, machine learning services, extensive storage options, and robust security measures.
Google Cloud Platform (GCP):
- Performance: GCP offers services such as NVIDIA A100, V100, T4, P100, and K80 GPUs. Enables them to work on resource allocation to optimise cost and performance.
- Pricing: GCP offers an on-demand price per second. It offers up to a 57% discount for committing to 1-3 years of usage. Additional charges for the storage and network may be applied.
- GPU Options: K80, P4, T4, P100, and V100 offer a range of performance options.
- Best for: GCP Service is best for specific AI and machine learning tasks.
- Features: GCP is best for features such as AI and ML training, data analytics, big data processing, rendering, and graphics-intensive applications.
Microsoft Azure:
- Performance: Microsoft Azure offers services such as NVIDIA A100, V100, T4, M60, and older GPU models. They also offer various networking options for high-priced computing and distributed ML workloads.
- Pricing: Accept the on-demand price based on the specific needs and requirements. It offers up to a 90% discount for interruptible workloads.
- GPU Options: There are various GPU options, including T4, A100, V620, M60, and MI25.
- Best for: Microsoft Azure is best for Azure machine learning and scientific computing that handles complex tasks
- Features: Microsoft Azure has various features such as data analytics and visualisation, HPC and large-scale simulations, enterprise applications, and workloads.
Pros and cons of each platform for different use cases
GPU Dedicated Server is the best platform to increase power and maintain speed on computing devices such as video rendering, data analytics, and machine learning. The GPU Dedicated Server is three cloud based providers named as Amazon Web Services, Google Cloud, Azure. In the above article, you learn about the difference between all these three platforms. Now we explain about the pros and cons of each GPU Dedicated Server platform.
Amazon Web Services (AWS):
AWS Pros:
- Most extensive cloud services: It provides on-premises public, private, hybrid, and multi-cloud cloud services.
- High Networking in Data Centers: Amazon’s cloud infrastructure provides the largest networking in the various data centres.
- Best cloud service experience: AWS provides public cloud services and continues to innovate and provide reliable services.
- User-friendly: AWS is an easier service than others and is also more suitable for small and medium businesses. AWS is a low-cost, free, and open-source solution.
- Ecosystem Integration: Deep integration with a vast array of AWS services such as SageMaker for ML and ECS/EKS for containers
- Flexible Pricing: Provide on-demand, reserved, spot instances, and savings plans.
- Third Party Software Solutions: AWS Marketplace provides a wide variety of third-party software that enhances your cloud services.
- Data Backup Facility: The vendor provides high-backup data services across multiple locations.
AWS Cons:
- Multiple Services options: There are multiple options to select from among the many cloud products, services, and features available that may create confusion.
- Expensive support: Technical support can be very costly and expensive.
- Cost: On-demand pricing is very expensive as compared to competitors for certain workloads.
Google Cloud Platform (GCP):
GCP Pros:
- Affordable Price: GCP offers an affordable price along with the best service.
- Available open-source support: GCP has tied up with the open-source community, which is involved in numerous projects with partners such as RedHat.
- Advanced machine learning and blockchain capabilities: The GCP platform has a huge database that supports advanced machine learning and blockchain capabilities.
- Integrated with the Tools: GCP is using tools like Gmail for Business, Spreadsheets, Forms, and Google Docs to integrate their services with the companies.
- Support multi-cloud deployments: The Google Cloud Platform supports multi-cloud deployments.
- Pricing: more user-friendly pricing and more straightforward.
- Security and compliance: Provide a high level of security and compliance.
GCP Cons:
- Limited number of cloud servers and data centres
- Limiting the usage of data in some regions
- It supports only limited enterprise solutions.
Microsoft Azure:
Microsoft Azure Pros:
- Superior enterprise support: it is hybrid cloud and on-premises services.
- Extensive Network of global data centres: It is the second-largest network of cloud servers that are accessible anywhere and anytime
- Integrated with Microsoft business applications: Various Applications integrated in this service include Microsoft 365, Azure Virtual Desktop, Microsoft SQL Server, and Power BI.
- Existing Microsoft licences integrate: It is easy to integrate existing Microsoft licences to prevent extra costs.
- Affordable cost: It is lower cost than AWS but costly than SMBs
- Supportable: Support Linux OS on a large scale.
Microsoft Azure Cons:
- Complexity: Azure service offers the service that is ineviatable for new users.
- Pricing: Price is very high on demand.
- Services: Technical Support service is very poor and there are huge complaints from the customers’ side.
Conclusion
Infinitive Host is the best GPU Dedicated Server that works for AI and Machine learning tasks. Select the right GPU dedicated server, complete regular tasks on a regular basis, and give the best and most reliable results. Choosing the right GPU Dedicated server provider depends on their basic needs.
AWS: machine learning, high-performance computing, and extensive integration with AWS services.
GCP: flexible pricing, custom machine types, and ideal for AI and ML workloads with strong TensorFlow integration.
Microsoft Azure: excellent hybrid cloud solutions, the best enterprise applications, and users heavily invested in the Microsoft ecosystem. Evaluate each cloud service provider based on factors related to your projects and make the decision based on performance needs, budget constraints, and integration requirements. Choose the best GPU Dedicated server platform that aligns best with and fulfils your business needs; check their previous performance, pricing, integration, and support factors that are relevant to your projects. Now it’s your choice which GPU Dedicated Server you want to choose to meet your specific business requirements. As per your requirements, Select the best GPU Dedicated server that fullfils your business needs.
Read More : Optimising GPU Server Performance for Deep Learning










