SELinux is an acronym for Security-Enhanced Linux, and it is a built-in access control mechanism for the Linux kernel. It enforces resource policies, which specify the amount of access users, applications, and services have to a system’s resources.
In detail, Security-Enhanced Linux (SELinux) is a Linux® system security architecture that enables administrators to have greater control over who has access to the system. It was initially created by the US National Security Agency (NSA) as a set of Linux kernel modifications utilising Linux Security Modules (LSM).
SELinux was made available to the open-source community in 2000 and was subsequently included in the mainline Linux kernel in 2003.
Working Procedure Of SELinux
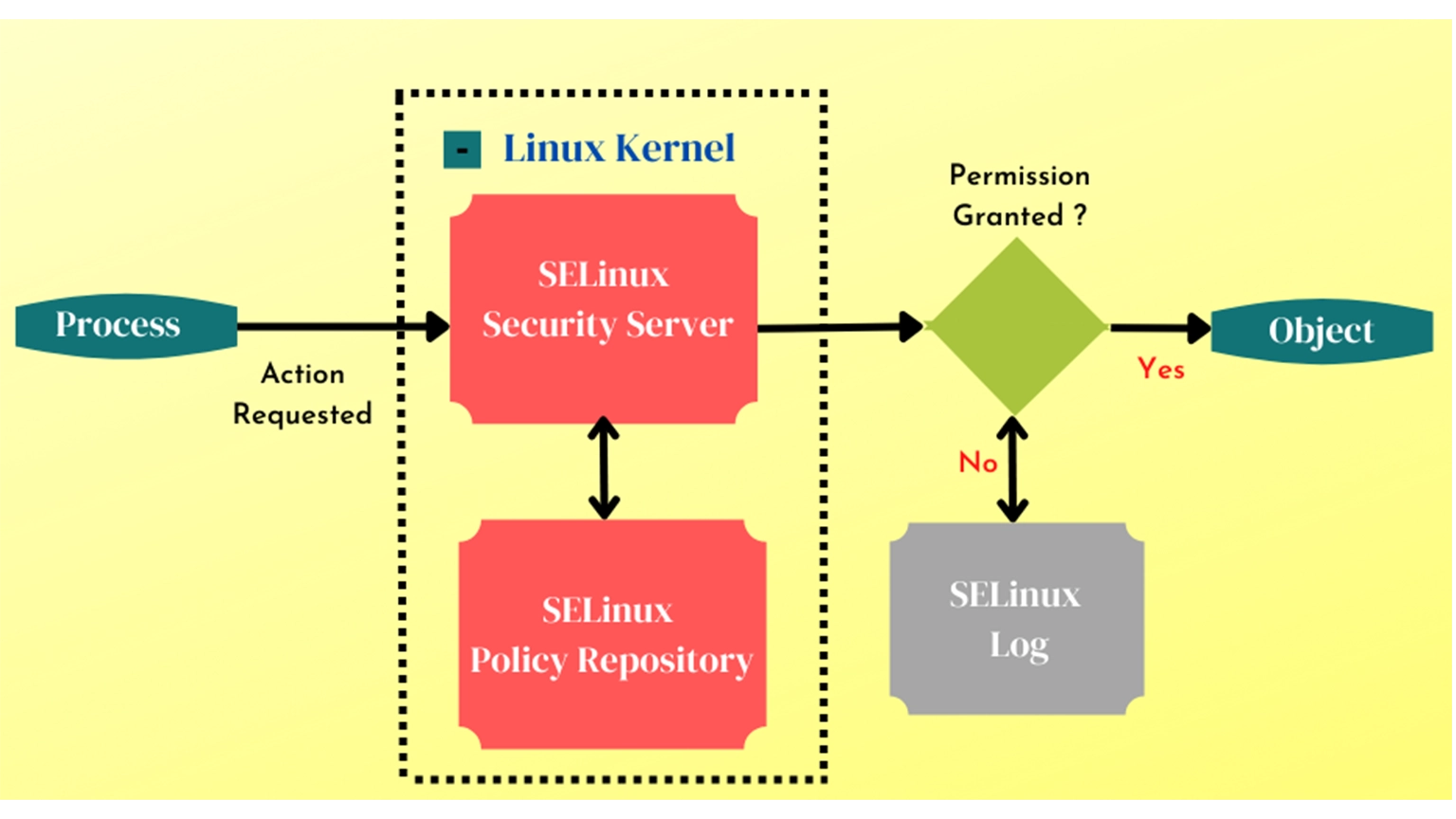
SELinux defines access restrictions for apps, processes, and files. Policies specify what can and cannot be accessed through the use of security policies, which are rules that SELinux obeys.
To determine if an application or process (referred to as a “subject”) has the proper rights to access an object (such as a file), SELinux consults an access vector cache (AVC).
SELinux requests the security server if it cannot make a judgement based on the cached permissions. The security server verifies the app’s or process’s and file’s security contexts. The SELinux policy is used to apply security context.
An “avc: denied” message will be available in /var/log.messages if permission is denied.
Setting Up SELinux In Your System
To keep your system safe, you may set up SELinux in various methods. Targeted policy or multi-level security are the most frequent (MLS).
The default policy is that encompasses a wide variety of processes, tasks, and services. Only government agencies utilise MLS, which is notoriously difficult to navigate.
You may determine the operating system that your system is meant to operate at by inspecting the /etc/sysconfig/SELinux file. The file will have a section indicating if SELinux is in permissive, enforcing, or disabled mode and the policy that is expected to be loaded.
Read More : A Beginner’s Guide To FirewallD in RHEL, CentOS and Fedora
Enabling SELinux
If your environment has disabled SELinux, you may re-enable it by modifying /etc/SELinux/config and setting SELINUX=permissive.
Rebooting after creating an empty file named.autorelabel in the root directory can compel the system to relabel the filesystem automatically. The permissive mode should be used if the system has too many mistakes so that the boot can proceed. Finally, reboot and change SELinux to enforce mode using /etc/SELinux.config and set-enforce
It is possible to control SELinux using graphical tools for those who are unfamiliar with the command line. SELinux is a built-in layer of security for Linux distributions that protects your system from external threats. In the event that your computer is ever hacked, you’ll be glad to have it running.
Methods For Resolving SELinux Errors
When an error occurs with SELinux, something has to be handled. It is quite probable that you are experiencing one of the following four typical issues:
- The labels are incorrect.
If your labelling is inaccurate, you may need to change it using the tools.
- A policy must be amended.
This might include notifying SELinux of a modification you’ve made or adjusting a policy. You may resolve this issue by utilising boo leans or policy modules.
- The policy is flawed.
The policy may have a flaw that needs to be fixed.
- Hackers have breached the system’s security.
There’s always the risk that a system might be hacked even if SELinux is used. It’s imperative that you take quick action if you believe this is true.
Read More : A Comprehensive Guide To A Bare Metal Hypervisor
Final Takeaway
SELinux (Security-Enhanced Linux) is user-space code that leverages kernel code (Linux Security Modules) to provide Mandatory Access Control (MAC) on system resources. Processes are contained within domains, which are analogous to sandboxes. Access to system objects and capabilities like files, message queues, semaphores, and networking is restricted per domain using the least privilege concept.
In SELinux, directories and files are designated with a permanent type distinct from the standard UNIX Discretionary Access Controls (DAC). This additional layer enables tighter control over object access: if an intruder obtains control of a process controlled by a user, access to all of that person’s files is not immediately allowed. SELinux may additionally regulate the type of access (read, write, create).